From Confusion to Clarity, My First Deep Dive into Cryptography
What I learned from a session by my senior Pragati Raj
It Started With a Simple Question
“Do you know how HTTP works? And why HTTPS is secure?”
That was the first thing my senior asked when the session began.
At that moment, I thought I had a basic idea. But when I actually tried to answer it in my head, I realized something uncomfortable. I use the internet every day, but I do not really understand how my data stays secure.
Before going further, let me introduce myself. I am Yugesh, a second year Computer Science and Engineering student specializing in Cybersecurity at DSCE. In this blog, I am sharing what I learned from my senior Pragati Raj during a pointblank session.
The Invisible Layer of the Internet
Every day, we log into accounts, send messages, and even make payments online. All of this feels normal. We do not stop and think about what is happening behind the scenes.
But the truth is, without cryptography, none of this would be safe.
Cryptography is what protects our data when it travels across networks. It makes sure that even if someone intercepts the data, they cannot understand it.
Two Sides of Security
One thing that stood out to me was that cryptology is not just about building systems. It also includes breaking them.
Cryptography focuses on creating secure methods like encryption, hashing, and digital signatures. Cryptanalysis focuses on finding weaknesses in those methods.
The important takeaway here is simple. No system is perfectly secure. The goal is to make attacks as difficult as possible.
Encoding vs Encryption
Before this session, I used to think encoding and encryption were somewhat similar. They are not.
Encoding is just a way of changing how data is represented. For example, Base64 encoding can be reversed easily. It is not meant for security.
Encryption, on the other hand, is designed to protect data. It converts readable information into an unreadable form, and only someone with the correct key can bring it back.
This difference may sound small, but it is very important.
From Old Methods to Modern Security
Earlier, people used simple techniques like Caesar cipher and substitution methods to protect data. These were useful in the past but are not secure today.
A famous real-world example is the Enigma machine used during World War II. It was once considered secure, but later it was broken, showing that no system is unbreakable.
Modern cryptography is much stronger and is based on mathematical algorithms.
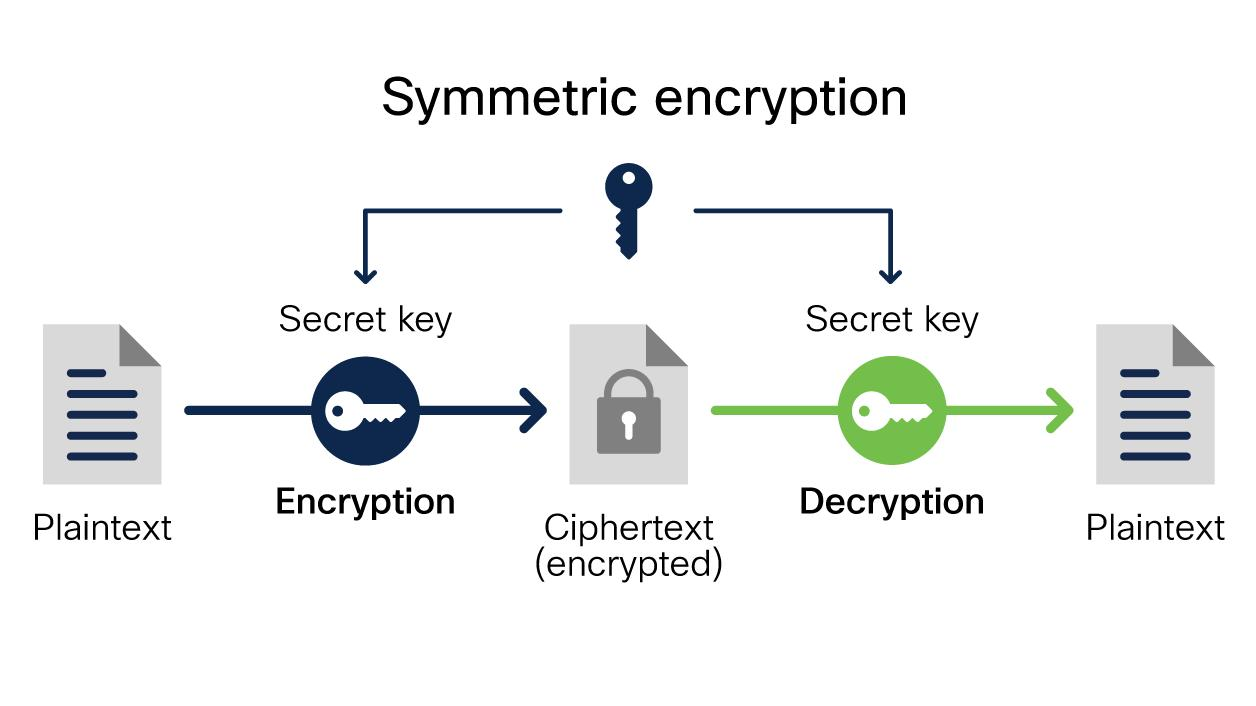
Symmetric Encryption
In symmetric encryption, the same key is used to encrypt and decrypt data.
This method is fast and efficient, which makes it suitable for handling large amounts of data. Algorithms like AES (Advanced Encryption Standard) are widely used today, especially AES-256.
There are different modes in AES like ECB, CBC, and GCM. Some modes like ECB are not secure, while GCM is commonly used because it provides better security.
The main problem here is key sharing. How do you safely share the key?
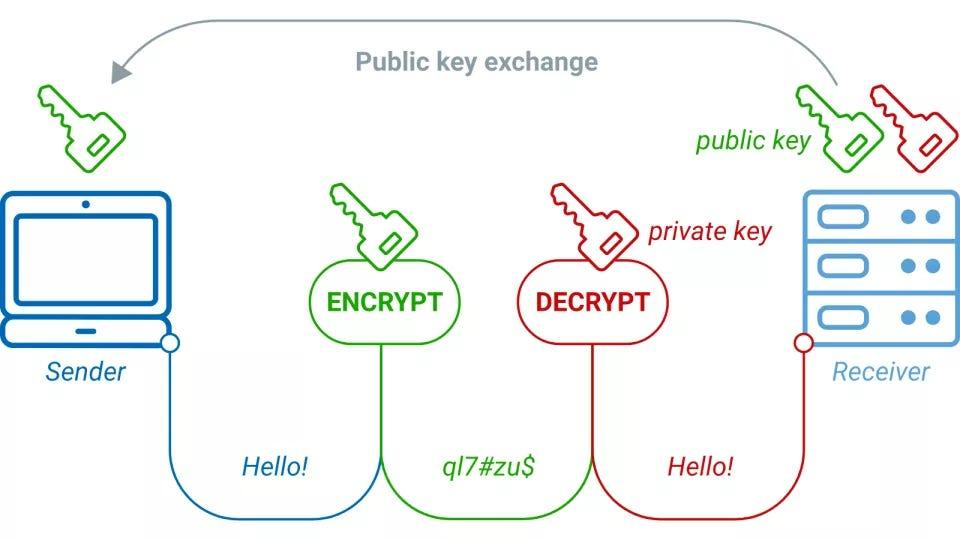
Asymmetric Encryption
This problem is solved using asymmetric encryption.
Instead of one key, we use two:
- Public key (can be shared)
- Private key (must be kept secret)
If I encrypt a message using someone’s public key, only they can decrypt it using their private key.
This is very secure, but slower compared to symmetric encryption.
Why HTTPS Uses Both
This was one of the most interesting parts of the session.
Instead of choosing one method, HTTPS uses both.
It uses asymmetric encryption at the beginning to securely exchange a key. After that, it switches to symmetric encryption for faster communication.
This combination gives both security and performance.
Proving That You Are Really You
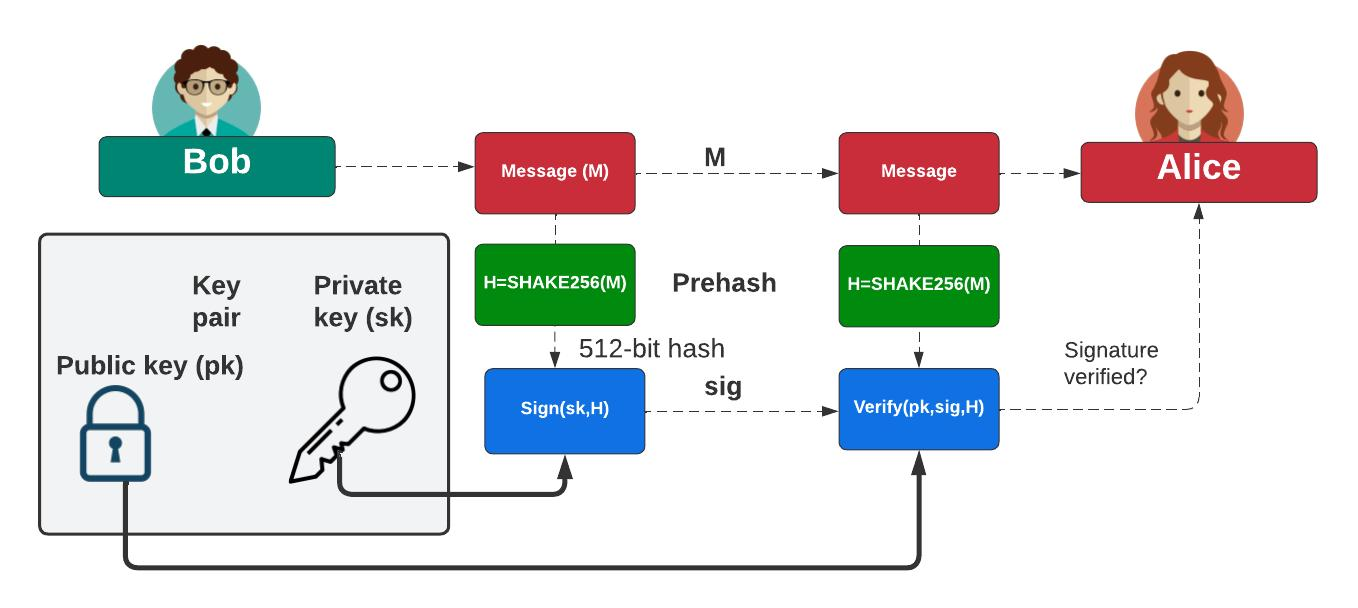
Another concept that I found interesting was digital signatures.
Here, instead of hiding data, we are proving authenticity.
The sender creates a hash of the data and encrypts it using their private key. The receiver can then verify it using the sender’s public key.
If everything matches, it proves that the data is genuine and has not been altered. It also ensures that the sender cannot deny sending it.
Why Hashing Is Everywhere?
Hashing is a one-way process that converts data into a fixed-size output.
Even a small change in the input creates a completely different output. This property is called the avalanche effect.
This is why passwords are not stored directly. Instead, their hashes are stored. When you log in, your input is hashed and compared.
To make this more secure, something called salt is added. This ensures that even if two users have the same password, their hashes will still be different.
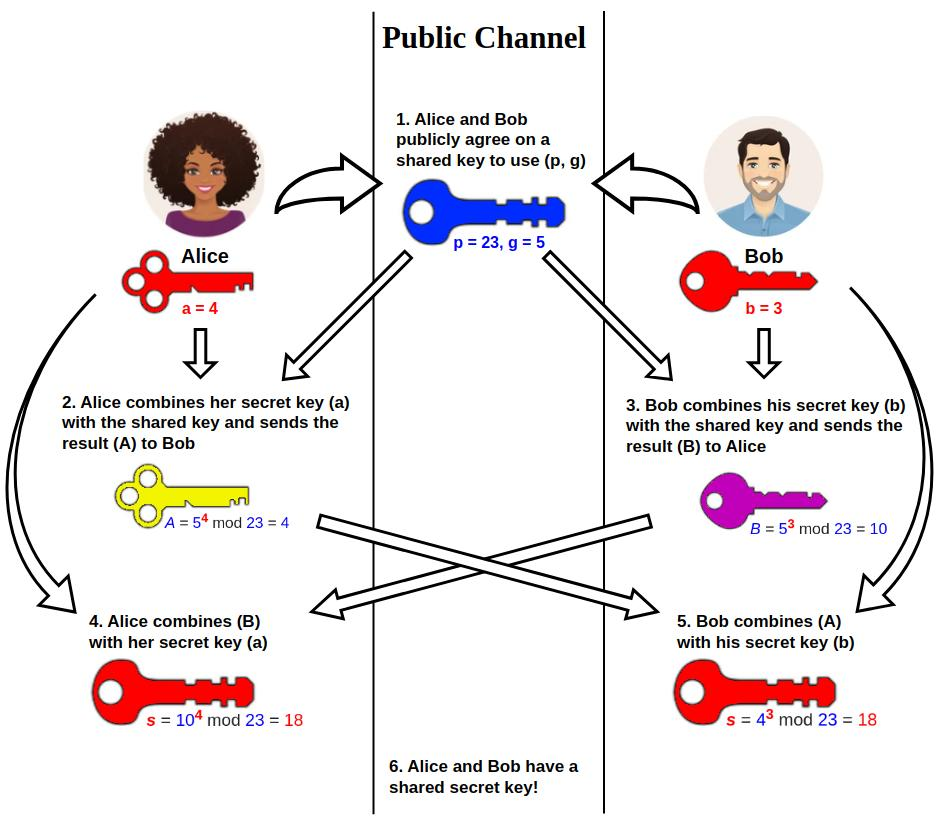
Sharing Secrets Without Sharing Them
Another concept that caught my attention was the Diffie-Hellman key exchange.
It allows two people to create a shared secret over an open network. Even if someone is listening, they cannot figure out the final key.
This idea feels almost counterintuitive, but it is one of the foundations of secure communication.
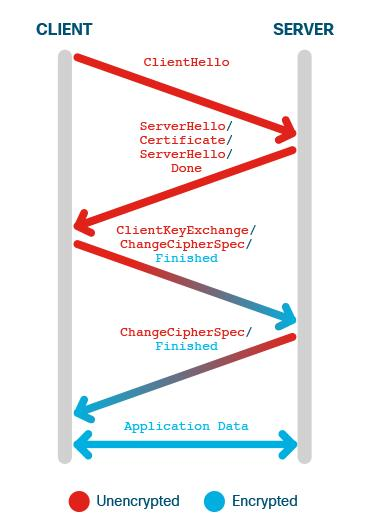
What Really Happens When You See HTTPS?
All these concepts come together in HTTPS.
When you open a website, the following happens:
- The browser sends a request to the server
- The server sends its certificate (which contains its public key)
- The browser verifies the certificate
- A secure key exchange happens (using asymmetric encryption)
- A session key is created
- All further communication uses symmetric encryption
This process is called the TLS handshake (a process to establish a secure connection).
Perfect Forward Secrecy
A very important concept in modern security is Perfect Forward Secrecy.
It ensures that even if a server’s private key is compromised in the future, past communication remains secure because each session uses a unique key.
More Than Just Theory
Towards the end of the session, we also discussed the CIA triad:
- Confidentiality (only authorized access)
- Integrity (data should not be changed)
- Availability (systems should be accessible)
These form the base of any secure system.
A simple real-world example is verifying a file using a checksum. When you download something like Ubuntu, you can compare its SHA-256 hash to ensure it has not been modified.
What I Took Away From This Session ?
The session ended with a practical suggestion from Pragati Raj. He told us to start using Linux and get comfortable with the terminal.
That made sense. Cybersecurity is not something you can learn only by reading. You need to explore, test, and understand systems deeply.
Conclusion
Before this session, HTTPS was just a small lock icon to me.
Now I see it differently. Behind that icon, there are multiple layers of security working together, including encryption, hashing, key exchange, and certificates.
This session made me realize that cryptography is not just an advanced topic. It is something every engineer should understand.
For me, this is just the beginning.
Thanks for reading.